Cloud Computing
Technology is changing rapidly with new inventions each passing day. Cloud Computing is one such technology trending these days. The word ‘cloud’ here refers to the internet. Thus it is an internet based technology.
What is Cloud Computing?
Cloud Computing is an internet based service that provides on demand access to shared computer resources and data. In other words, cloud computing means delivery of hosted services and resources over the internet. These resources include storage, server, network and applications. These resources can be quickly equipped and can be freed easily. Virtualization is the driving force behind cloud computing.
What is Virtualization?
Virtualization means the creation of virtual resources rather than actual resources like hardware, operating system, storage, network etc. These virtual resources act as a replica of the actual resources. The common example of virtualization is the partition of the hard drive to create separate hard drives. In virtualization, there are two types of machines host machine and the guest machine. Host machine is the real physical machine on which virtualization takes place while the guest machine is the virtual machine. Following are the types of virtualization:
- Hardware Virtualization
- Operating System Virtualization
- Desktop Virtualization
- Storage Virtualization
- Network Virtualization
VMware and Virtual Box are the examples of tools that use the concept of virtualization.
Characteristics of Cloud Computing
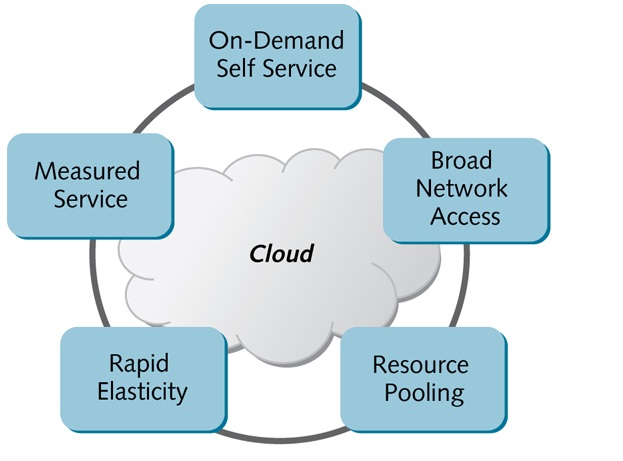
Following are the characteristics of cloud computing as identified by NIST(National Institute of Standard and Technology):
- On-demand self-service: A consumer can provision for cloud computing services without interaction with service providers.
- Broad network access: Cloud Computing resources can be accessed from a range of devices like desktops, laptops, smartphones etc.
- Resource pooling: Clouding Computing creates a shared pool of resources that can be accessed by a consumer as and when required.
- Rapid Elasticity: Rapid Elasticity refers to the scalability of resources according to the demand.
- Measured Service: The usage of cloud resources can be monitored, controlled and reported for billing and access control.
Cloud Computing Service Model or Cloud Computing Services
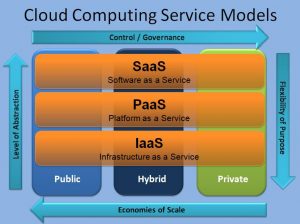
Cloud Computing Services are categorized as :
- Infrastructure as a Service(IaaS)
- Platform as a Service(PaaS)
- Software as a Service(SaaS)
Infrastructure as a Service(IaaS)
Infrastructure as a Service provides virtual computing resources such as storage, server, virtual machines and network over the internet. A third party provider provides this infrastructure to the consumer.
Platform as a Service(PaaS)
Platform as a Service allows the consumer to deploy applications on the cloud infrastructure. A consumer is not responsible for the underlying cloud infrastructure.
Software as a Service(SaaS)
Software as a Service enables the user to use the deployed applications running on the cloud infrastructure. The consumer is not responsible for managing the underlying infrastructure and the applications.
Cloud Deployment Models
Private Cloud
Private Cloud is provided for a single organization with multiple consumers. It is operated by the organization itself or by a third party. It may be operated within the premises or off the premises.
Public Cloud
Public Cloud is for public use or a large organization and is owned by a third party provider selling cloud services.
Hybrid Cloud
Hybrid Cloud is a combination of two or more distinct clouds that retain their unique entity. It is used for sensitive data and strategic applications.
Community Cloud
It is a type of private cloud for users with specific demands. It has several stakeholders. It is managed by the organization or by a third party provider.
Examples of cloud services
- Apple iCloud
- Amazon EC2
- Microsoft Azure
- Google Drive
Advantages of Cloud Computing
- It is cost effective
- It is based on pay per use method
- Improved security
- It is much more reliable and manageable
- It is flexible, scalable and also environment-friendly as it reduces carbon footprint
Drawbacks of Cloud Computing
- Security and privacy issues while using services from third party providers
- As it is an internet based service, it faces the risk of downtime i.e. internet breakdown or connection problems
- It is prone to cyber attacks
- Vendor lock-in – It is a situation when a consumer wants to switch to other vendor’s services but cannot easily shift without paying a considerable cost.
Cloud Computing Services are rapidly changing with new advancements each day. It is important for each internet user to know the use of this technology. Cloud Computing subject should be mandatory in the curriculum of computer science and information technology engineering streams. It is also beneficial in higher studies of computer science and information technology. M.Tech thesis in Cloud Computing is also a good choice for scholars. Therefore it should be reached to wider internet users.
Cloud Computing Security
Cloud Computing security refers to set of policies and measures deployed to protect cloud infrastructure and the underlying data and applications. It is a part of information security. Cloud Computing Security is needed as there are certain security concerns regarding security and privacy of the users and their data. Cloud Computing gives users the ability to store and process data at third-party data centers. Cloud Computing provides cloud service models -IaaS, PaaS, and SaaS along with cloud deployment models – public, private, hybrid, and community cloud.
The cloud computing security issues may be at the provider end or at the customer end. It is the responsibility of the provider that their infrastructure is secure and also user’s data and the information is protected. Users should also secure their data with strong authentication measures. Data stored in the public cloud is sensitive to third-party attacks or the insider attacks. Often cloud service providers store more than one customer’s data on a single server to reduce costs and maintain efficiency. Due to this, there are chances of one user’s data being exposed to another user. For handling such situation, cloud service providers must provide proper data isolation and logical segregation of data.
Controls in Cloud Security
Following are the controls in Cloud Security Architecture:
- Deterrent Control – These controls try to reduce outside attacks on the cloud system.
- Preventive Control – These controls strengthen the cloud system by eliminating all the possible vulnerabilities.
- Detective Control – These controls are intended to detect any incident which may lead to the attack on the system.
- Corrective Control – Corrective controls try to minimise the damage caused by the incident or attack.
Topics in Cloud Security for research and thesis
Following is the list of current research and thesis topics in Cloud Computing Security:
- Virtualization
- Encryption
- Cloud Security Dimensions
- Denial of Service(DoS)
- Identity Management
- Data Security
- Data separation
- DDoS Attacks
Virtualization
Virtualization is an important concept in cloud computing and it refers to the process of creating a virtual version of something rather than real like a server, storage, and networks. Cloud Computing is based on this concept of virtualization. Hardware Virtualization means the creation of virtual machines that can act and work like a real computer with an operating system. Hardware Virtualization is of two types – Full Virtualization and Paravirtualization. The actual machine on which virtualization is done is referred to as host machine while the virtual machine is referred to as the guest machine. It is a very good topic for the thesis. Students looking for cloud computing thesis topic suggestion can opt this topic for their work.
Encryption
Encryption is a method of protecting the data by sending the data in some other form. In order to provide more protection and privacy to data, cloud computing uses advanced encryption algorithms. Another measure known as crypto-shredding is also applied in which keys are deleted when there is no need to use data. The types of encryption employed in cloud computing security include – Fully homomorphic encryption and Searchable Encryption.
Cloud Security Dimensions
The Cloud Security Controls are selected and implemented in accordance with the amount of risk, threat, and vulnerabilities. The cloud security concerns can be grouped according to their amount of risk. There is a software named Cloud Access Security Brokers(CASB) in between cloud service users and cloud applications that monitors all the cloud security policies and also enforce security policies.
Denial of Service(DoS)
Denial of Service(DoS) is a type of attack in which an intruder makes resources unavailable to users by disrupting the services connected to the internet. The attacker tries to overload the system with surplus requests and also block the incoming genuine requests. There are various types of DoS attacks like Distributed DoS attack, Application layer attack.
Identity Management
Identity Management is the process of providing authorized access to the cloud services. Every user is provided with a unique ID and password for access to the cloud system. The main purpose of Identity Management is to verify that whether a user should be allowed access to cloud system or not. It ensures that only authorized users are granted access to the system.
Data Security
Security of data in Cloud-based services is a major concern. Often data is exposed particularly in public cloud due to some loopholes and vulnerabilities. For providing security and privacy of data, the encryption method is used in cloud computing. Other data security issues include data replication, data loss due to breach, and security of data in public cloud platform.
Data Separation
Due to multi-tenant nature of public cloud and other data security concerns, users try to avoid this platform. Due to sharing of cloud resources like virtual machine between users, data separation is almost impossible. Another aspect of data separation is geolocation. Enterprises should ensure that the geolocation for data storage is a trusted location. Tenancy and geolocation are the major factors in Data Separation.
DDoS Attacks
DDoS stands for Distributed Denial of Service and is a type of Denial of Service Attack in which malicious traffic comes from multiple devices. This makes it difficult to differentiate genuine traffic from the malicious traffic. There is another type of DDoS attack known as Application layer DDoS attack in which the application layer of the OSI model is targeted by the attacker.
These are the current cloud computing thesis and dissertation topics. Contact Techsparks for any type of M.Tech thesis help in cloud computing.
For more details Contact Us. You can call us on this number +91-9465330425 or drop an email at techsparks2013@gmail.com for any type of dissertation help in India. You can also fill the query form on the website.
You can also visit our website Techsparks and follow us on Pinterest, Facebook, Twitter, YouTube and Linkedin for latest thesis blog.



Leave a Reply